I often get asked how it was that I managed to make my way into the information/cyber security field. I want to preface this by saying that I definitely don’t think that my route into cybersecurity is the only one. There are certainly many! Probably, there are many other routes which are much better than the one I took. But for those who might ask, here is my story all the same.
The Beginning
I was a huge fan of the movie Live Free or Die Hard when I was an early teen. It had just come out around that time, and it contained all the right things to keep my young interest. There were awesome explosions, there were shootouts, there was parkour (my favorite). There was even a whole scene where Bruce Willis fights a fighter jet, that was freaking sweet!
But within that film, was something that was all but new to me. The villain of the film was working with a loose network of hackers (some working for him, others against) to try and take down the infrastructure of the United States. In the film they called it a ‘fire sale’. The antagonist’s motivation was to get back at a broken system that had ignored his calls for change.
This was all interesting to me. But I had no frame of reference for it. I wasn’t born into a family of computer scientists. I didn’t attend a great STEM school. I had no background in these things. Now, I had always been quite technically minded. I was a huge fan of Legos growing up. I remember spending days – going to sleep – and waking up to continue building a new creation. When I was a kid I had often identified my dream jobs as “pilot” and “Lego master builder” (the people who design Lego sets).
I was also a huge fan of spy fiction…
Splinter Cell
It was also around this time that I fell into the world of Tom Clancy’s Splinter Cell. For a young kid, it was easy for me to understand the principles of light and shadow, the foundational elements of stealth. I clearly remember night after night, sneaking around with my friends in our neighborhood, taking turns chasing one another; and trying to avoid detection.
These ‘spy games’ led me to learn more, and to seek out additional information about the motivations and intentions behind espionage. Suddenly I understood a lot more about why information was useful, and how to acquire it.
High School
I had been a member of the Civil Air Patrol since before I was a teen. If you’ve never heard of it; the Civil Air Patrol (CAP) has a cadet organization for kids between 12-21 (with an adult wing as well!). I enjoyed my time in the Civil Air Patrol, and from being a member there, decided to join the AFJROTC (Air Force Junior Reserve Officer Training Corps) out of my local high school.
I loved this program, even more than I had loved the Civil Air Patrol. We had awesome instructors, and learned a ton. Better still, being a part of this program helped me to see a path to joining the Air Force as an officer. Around the start of my sophomore year I set off on a mission to get selected for the Air Force Academy.
Air Force Academy
The United States Air Force Academy is exceptionally hard to get into. You need to be nominated by a member of congress, you’ll go before a selection panel; and even if you meet the bar, it’s likely you still won’t go. There are only a few spots every year per state, so if someone else has a better packet than you, or if they’ve been waiting longer, they’re likely to pass you.
I knew that if I wanted any good shot at getting into USAFA, I was going to need to do everything right.
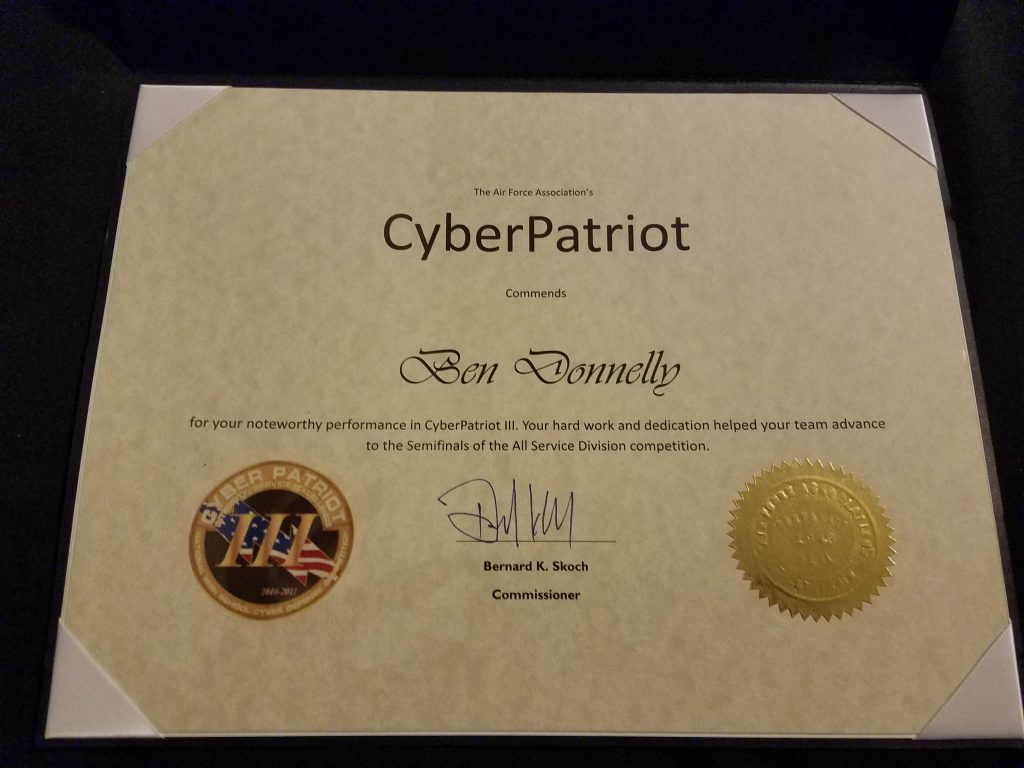
Cyberpatriot III
Up until this point, I had very little technical background in computers. I was technically minded, that was for sure. But the inner workings of computers has not yet made it to my list of ‘most interesting subjects.’ One of the instructors in my AFJROTC program put out a call for members to join a team for a small competition called ‘Cyberpatriot’. It was going into its 3rd year. This year, for the first time ever, there would be a competition that included teams not just from cadet organizations, but from general tech student teams outside of ‘military related programs’.
All the same, my cadet program was putting together a team for the second year. We had done fine last year, and I think we went in without an intention to win. We simply wanted a good opportunity to train in a skill that we knew was being demanded by the DOD (as well as the private sector).
We would get that training, and much more. Just a handful of months later I was sitting on a plane on my way to Orlando for the national semi-finals. The field was still relatively small, but growing rapidly. That year our team made the semi-finals, where a better team from Clearfield Utah would pass us and go onto the finals.
I learned a ton that year. I remember coming back from nationals with a renewed sense of urgency. The mission felt real to me, and I was prepared to learn more.
Cyberpatriot IV
We returned the next year, this time making it all the way to the national finals. We took second nationally in our division – and first in the AFJROTC. I remember feeling this year fly by. I had come in entirely without a background in cybersecurity, but by the time nationals rolled around for Cyberpatriot IV, I was starting to pass some of the professional mentors we had brought in to train us.
I was absolutely loving the cybersecurity mission, and I honestly just wanted to learn more. I spent much of my free time trying to dig deeper into various related disciplines. I started teaching myself to code, I wrote websites, learned about database, how to write SQL, how to run a LAMP stack. I started dabbling in offensive techniques. I distinctly remember figuring out how to take over my fellow Cyberpatriot team member’s computers during our training. It was a blast!
Heading to College
I did actually get the nomination by my local congresswoman to the Air Force Academy. I was even accepted to USAFA prep, with an expectation that I would be accepted for the full ride the next year (there was someone ahead of me in the queue). I didn’t go. This had been my dream for quite a number of years. Tragedy in my family took my father from me; and so I decided to stay home and do college myself for a few years.
So, rather than go to one of the most prestigious schools in the world, I instead went to the local community college. I chose that school on purpose (as weird as it sounds) because they were the only local college with a program that mirrored my interests. You may be well aware that there are very few good programs in Cybersecurity, even today… it was worse back then.
I kept training on my own time, and learning under my own power. My classes were largely boring, and I tended to blow them off. I was pretty advanced by this point in comparison to many of the students. Though to say that I was the only student there who was relatively advanced would be incorrect. A few of the other kids who had been on Cyberpatriot teams in my school district were also in those classes, we all tended to know more, and to hang out together. Quickly thereafter, those other students who had the background in cybersecurity from high school found jobs working IT for local companies. My story would take a slightly different turn.
Heading to NetWars
SANS hosted its (to my knowledge) first ever NetWars tournament of champions at SANS CDI in 2012. They put out information on this upcoming tournament on their website, which I just happened to stumble on. They mentioned that they would be inviting previous winners of NetWars as well as high performing students in Cyberpatriot. This was when we were just coming out of Cyberpatriot IV where my team had that 2nd place title nationally – yet I had not been invited.
So I did the only logical thing one could do (a bit of sarcasm here) and emailed SANS asking if I could come. To my surprise, I heard back almost immediately; it was a yes! SANS wouldn’t cover room and board or anything, but if I showed up at the conference, I could compete without paying the entry fee.
I think that it was this moment that helped me start my career in infosec. Having gone out of my way to ask if I could attend this conference – and having been accepted – I now flew myself to Washington DC in the middle of the winter to compete in my first ever ‘red team’ event.
Competition & Internship
I did pretty decently in the competition. As mentioned, this was the first time I had actually done any ‘red teaming’ outside of practice with friends, and from that I took 24th/~200 competitors. I would come back the next year to win NetWars at SANSFIRE 2013; and again as level 5 OPFOR at a future tournament of champions (in which I hacked the scorebot for fun).
But it wasn’t the competition that really kicked things off for me. I think it was my age. I was fresh out of high school at the time, and having flown myself to DC, was surrounded by infosec professionals from all walks of life. I stuck out like a sore thumb to say the least.
I will always remember the first night during which I was accidentally offered alcohol at a meet and greet, simply because nobody assumed someone as young as me would be there (still under 21). The SANS folks were awesome, and took me under their wing for the conference. They allowed me to sit in on a pentesting course, through which I was offered the first of three internships I would be offered that weekend. I took that role right then and there.
Within a year I would be moving from ‘intern’ to full-fledged ‘pentester’.
Security Engineering
I’m often asked how I made it as a pentester so early on in my career. I think the more interesting question is what I went on to do next. Pentesting is really cool, and for sure I’m not done with it. But when you run the same attacks day in and day out for years, it can start to get a little boring.
If I was to offer any advice for newcomers to infosec, it would be this: Don’t ignore the awesomeness of defense. Knowing how to hack is really cool. Once you master it, you’ll find it’s not necessarily as creative as it could be. This isn’t to say there aren’t really creative, really awesome pentesting teams out there. But for many targets, for many pentests, you’ll find that the same old tricks work again and again. Pentesting for companies like that can start to look less like a sweet adventure, and more like QA testing.
For the time being at least, I’m focusing much of my energy on security engineering. Certainly still keeping it up with some red cell activity from time to time. But learning a lot more about software development, and how to bring creative thought to engineering away classes of problems, rather than exploiting them.